Használati útmutató Sitecom WLR-4003
Olvassa el alább 📖 a magyar nyelvű használati útmutatót Sitecom WLR-4003 (73 oldal) a router kategóriában. Ezt az útmutatót 3 ember találta hasznosnak és 2 felhasználó értékelte átlagosan 4.5 csillagra
Oldal 1/73

WLR- 4003
Wireless Gigabit Router N300
(802.11 b/g/ n)

User Manual
TABLE OF ONTENTSC
1 KEY FEATURES .................................................................................... 4
2 PACKAGE CONTENTS ........................................................................... 5
3 CAUTIONS .......................................................................................... 6
4 PRODUCT LAYOUT ............................................................................... 7
5 SYSTEM REQUIREMENTS .................................................................... 10
6 WLR-4003 PLACEMENT ....................................................................... 10
7 SETUP LAN, WAN .............................................................................. 11
8 PC NETWORK ADAPTER SETUP ............................................................ 12
9 BRINGING UP THE WLR- 4003 ............................................................. 16
10 INITIAL SETUP WLR-4003 ..................................................................16
11 CONFIGURATION WIZARD .................................................................. 25
12 WIRELESS SETTINGS ......................................................................... 27
13 FIREWALL SETTINGS ......................................................................... 39
14 ADVANCED SETTINGS ........................................................................ 45
15 TOOLBOX SETTINGS .......................................................................... 55
16 APPENDIX ........................................................................................ 67
Revision 1.0
© Sitecom Europe BV 2012
Note: All the information contained in this manual was correct at the time of
publication.
However, as our engineers are always updating and improving the product, your
device‟s software may have a slightly different appearance or modified
functionality than presented in this manual.

Introduction
Congratulations on your purchase of the WLR- Wireless Gigabit Router 4003
N300. The WLR- is compliant with 802.11n and up to 6 times faster than 4003
standard 802.11g based routers while still being compatible with 802.11g &
802.11b devices. The WLR- is not only a Wireless Access Point, but also 4003
doubles as a 4-port full-duplex Gigabit switch that connects your wired-
Ethernet devices together at 10/100/1000 Mbps speeds.
At 300 Mbps wireless transmission rate, the Access Point built into the Router
uses advanced MIMO (Multi-Input, Multi-Output) technology to transmit
multiple streams of data in a single wireless channel, giving you seamless
access to multimedia content. The robust RF signal travels farther, eliminates
dead spots and extends the network range. For data protection and privacy,
the WLR- encodes all wireless transmissions with WEP, WPA, or WPA2 4003
encryption.
With the inbuilt DHCP Server & powerful SPI firewall, the WLR- protects 4003
your computers against intruders and most known Internet attacks and also
provides safe VPN pass-through. With the incredible speed and QoS function of
802.11n the WLR- is ideal for media-centric applications like streaming 4003
video, gaming, and VoIP telephony to run multiple media-intense data streams
through the network at the same time, with no degradation in performance.
This product can be used safely in the countries listed below:
This product complies with the following European Union regulations:
4
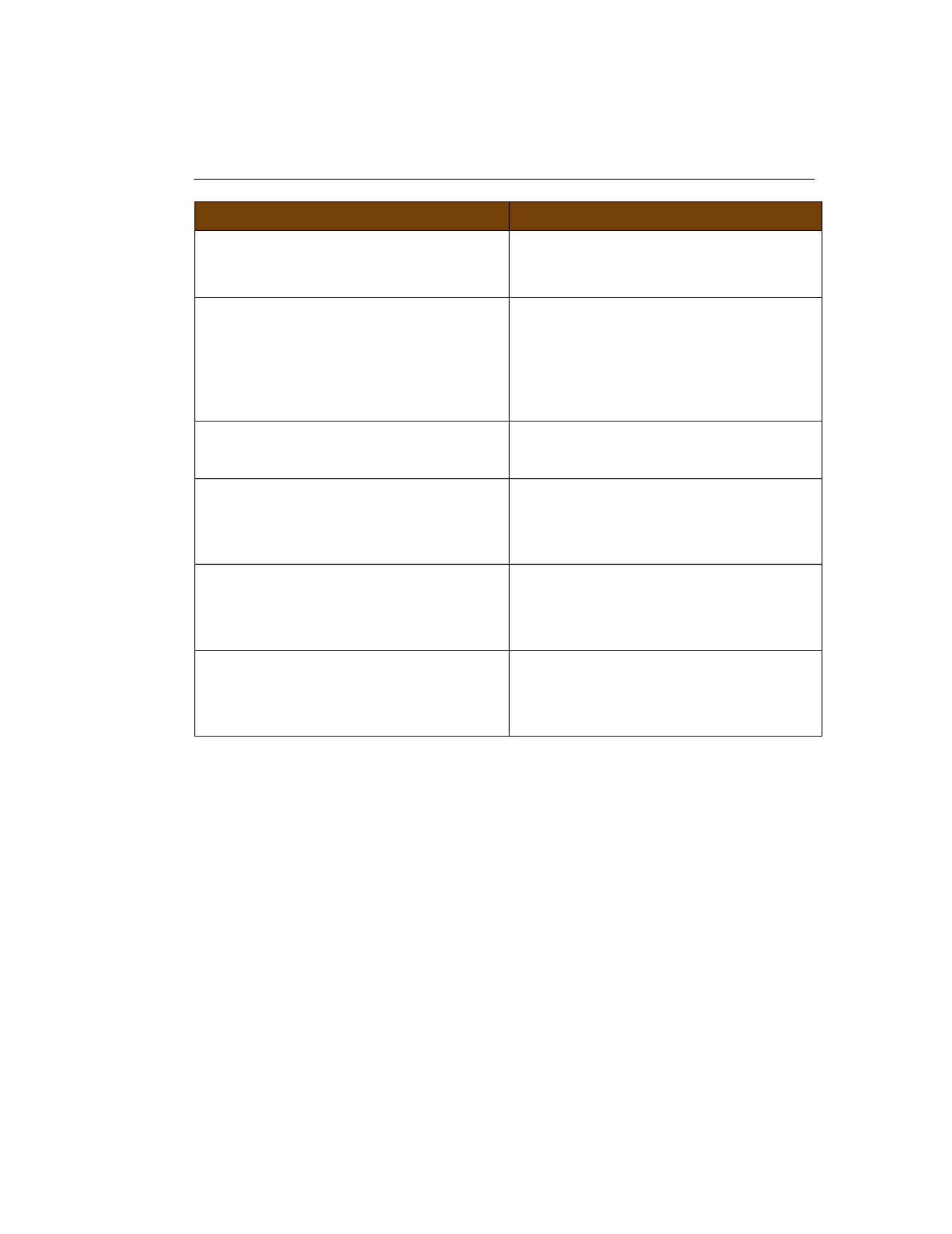
1 Key Features
Features
Advantages
Incredible Data Rate up to
300Mbps*
Heavy data payloads such as
MPEG video streaming
IEEE 802.11n Compliant and
backwards compatible with
802.11 b/g
Fully Interoperable with IEEE
802.11b / IEEE802.11g
compliant devices with legacy
protection
Four 10/100/1000 Mbps gigabit
Switch Ports (Auto-Crossover)
Scalability, extend your network.
Firewall supports Virtual Server
Mapping, DMZ, IP Filter, ICMP
Blocking, SPI
Avoids the attacks of Hackers or
Viruses from Internet
Support 802.1x authenticator,
802.11i (WPA/WPA2, AES), VPN
pass-through
Provide mutual authentication
(Client and dynamic encryption
keys to enhance security
WDS (Wireless Distribution System)
Make wireless AP and Bridge
mode simultaneously as a
wireless repeater
* Theoretical wireless signal rate based on IEEE standard of 802.11b, g, n chipset used. Actual
throughput may vary. Network conditions and environmental factors lower actual throughput rate.
All specifications are subject to change without notice.
5
2 Package Contents
Open the package carefully, and make sure that none of the items listed
below are missing. Do not discard the packing materials, in case of return;
the unit must be shipped back in its original package.
1. The WLR- Router 4003
2. A 110V~240V to 12V 1A Switching Power Adapter
3. A Quick Install Guide
4. A CD (User‟s Manual)
5. A Warranty card
6. An UTP cable

6
3 Cautions
This router‟s design and manufacturer has your safety in mind. In order to
safely and effectively use this router, please read the following before usage.
3.1 Usage Cautions
The user should not modify this router. The environmental temperature
should be within +5 ~ +35 degrees Celsius.
3.2 Power
The router‟s power voltage is DC 12V 1A.
When using this router, please connect the supplied AC adapter or AC adapter
cable to the router‟s power jack. When placing the adapter cable, make sure
it can not get damaged or be subject to pressure. To reduce the risk of
electric shock, unplug the adapter first before cleaning it. Never connect the
adapter to the router in a humid or dusty area. Do not replace the adapter or
cable‟s wire or connector.
3.3 Repair
If the router has a problem, you should take it to an appointed repair centre
and let the specialists do the repair. Never repair the router yourself, you
might damage the router or endanger yourself.
3.4 Disposing of the Router
When you dispose of the router, be sure to dispose it appropriately. Some
countries may regulate disposal of an electrical device, please consult with
your local authority.
3.5 Others
When using this router, please do not let it come into contact with water or
other liquid If water is accidentally spilled on the router, please use a dry s.
cloth to absorb the spillage. Electronic products are vulnerable, when using
please avoid shaking or hitting the router, and do not press the buttons too
hard.
- Do not let the router come into contact with water or other liquid.
- Do not disassemble the r, repair the router or change the design of the route
router, any damage done will not be included in the repair policy.
- Avoid hitting the router with a hard object, avoid shaking the router and
stay away from magnetic fields.
- If during electrostatic discharge or a strong electromagnetic field the
product will malfunction, unplug the power cable. The product will return to
normal performance the next time it is powered on.

7
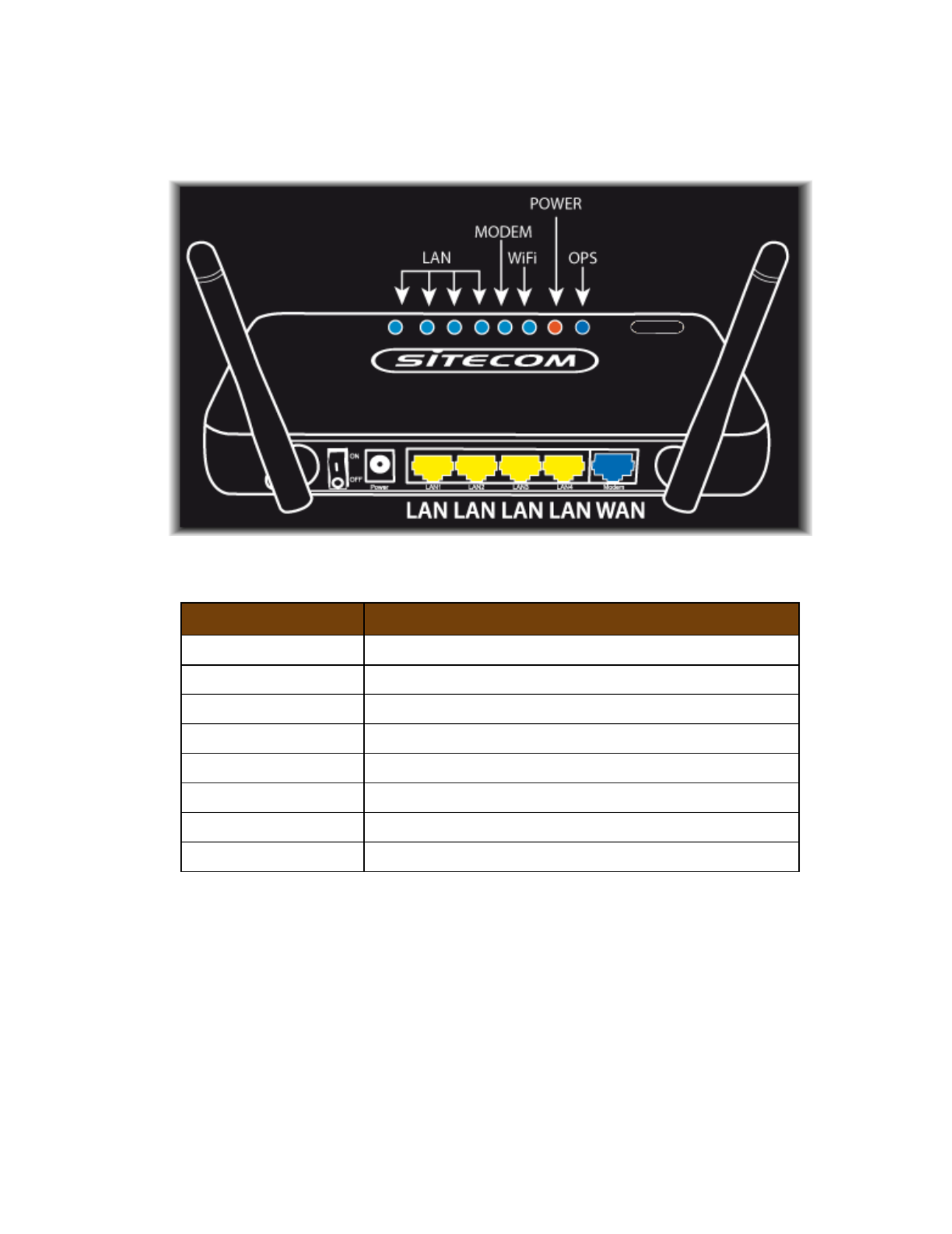
4 Product Layout
Port
Description
Power connector
Connect the 12V DC adapter to this port
LAN (Yellow)
Connect your PC‟s or network devices to this port
WAN ( ) Blue
Connect your ADSL/Cable modem to this port

8
Backlabel
The backlabel describes the IP address, login details, SSID, security code and
WPS button functionality.
Button
Description
OPS BUTTON
Press 2 seconds for OPS mode
Press 10 seconds to reset the router
Press 15 Seconds to reset the router to factory defaults.
9
LED Definition
From left to right.
Port
Description
LAN ( ) Blue
Shows the cable is connected.
LAN ( ) Blue
Shows the cable is connected.
LAN ( ) Blue
Shows the cable is connected.
LAN ( ) Blue
Shows the cable is connected.
WAN ( ) Blue
Shows the cable is connected.
WiFi ( ) Blue
Shows WiFi activity.
Power ( ) Red
Shows the device is turned on.
OPS ( ) Blue
Shows OPS activity.

10
5 System Requirements
To begin using the WLR- , make sure you meet the following as minimum 4003
requirements:
PC/Notebook.
Operating System Microsoft Windows XP/Vista/Seven –
1 Free Ethernet port.
WiFi card/USB dongle (802.11 b/g/n) optional. –
External xDSL (ADSL) or Cable modem with an Ethernet port (RJ-45).
PC with a Web-Browser (Internet Explorer, Safari, Firefox, Opera)
Ethernet compatible CAT5 cables.
6 R-4003 Placement WL
You can place the WLR- on a desk or other flat surface, or you can mount 4003
it on a wall. For optimal performance, place your Wireless Broadband Router
in the center of your home (or your office) in a location that is away from any
potential source of interference, such as a metal wall or microwave oven. This
location must be close to a power connection and your ADSL/Cable modem.

11
7 Setup LAN, WAN
WAN connection:
LAN connection:

12
8 PC Network Adapter setup
Windows XP
Enter [Start Menu] select [Control panel] select [Network].
Select [Local Area Connection]) icon=>select [properties]

14
Windows Vista/Seven
Enter [Start Menu] select [Control panel] select [View network status
and tasks] -> select [Manage network connections].
Select [Local Area Connection]) icon=>select [properties]

15
Select [Internet Protocol Version 4 (TCP/IPv4)] =>Click [Properties].
Select the [General] tab.
The router supports [DHCP] function, please select both [Obtain an IP address
automatically] and [Obtain DNS server address automatically].

16
9 Bringing up the WLR-4003
Connect the supplied power-adapter to the power inlet port and connect it to
a wall outlet. The WLR- automatically enters the self-test phase. During 4003
self-test phase, the Power LED will be lit continuously to indicate that this
product is in normal operation.
10 Initial Setup WLR-4003
LOGIN procedure
1. OPEN your browser (e.g. Internet Explorer).
2. Type in the address bar and press [Enter] http://192.168.0.1

17
3. Type user name and password. The default username is admin, the
password can be found on the back label on the bottom of your router.
4. Click . OK
5. You will see the home page of the WLR- . 4003
The System status section allows you to monitor the current status of your router
the UP time, hardware information, serial number as well as firmware version
information is displayed here.
18
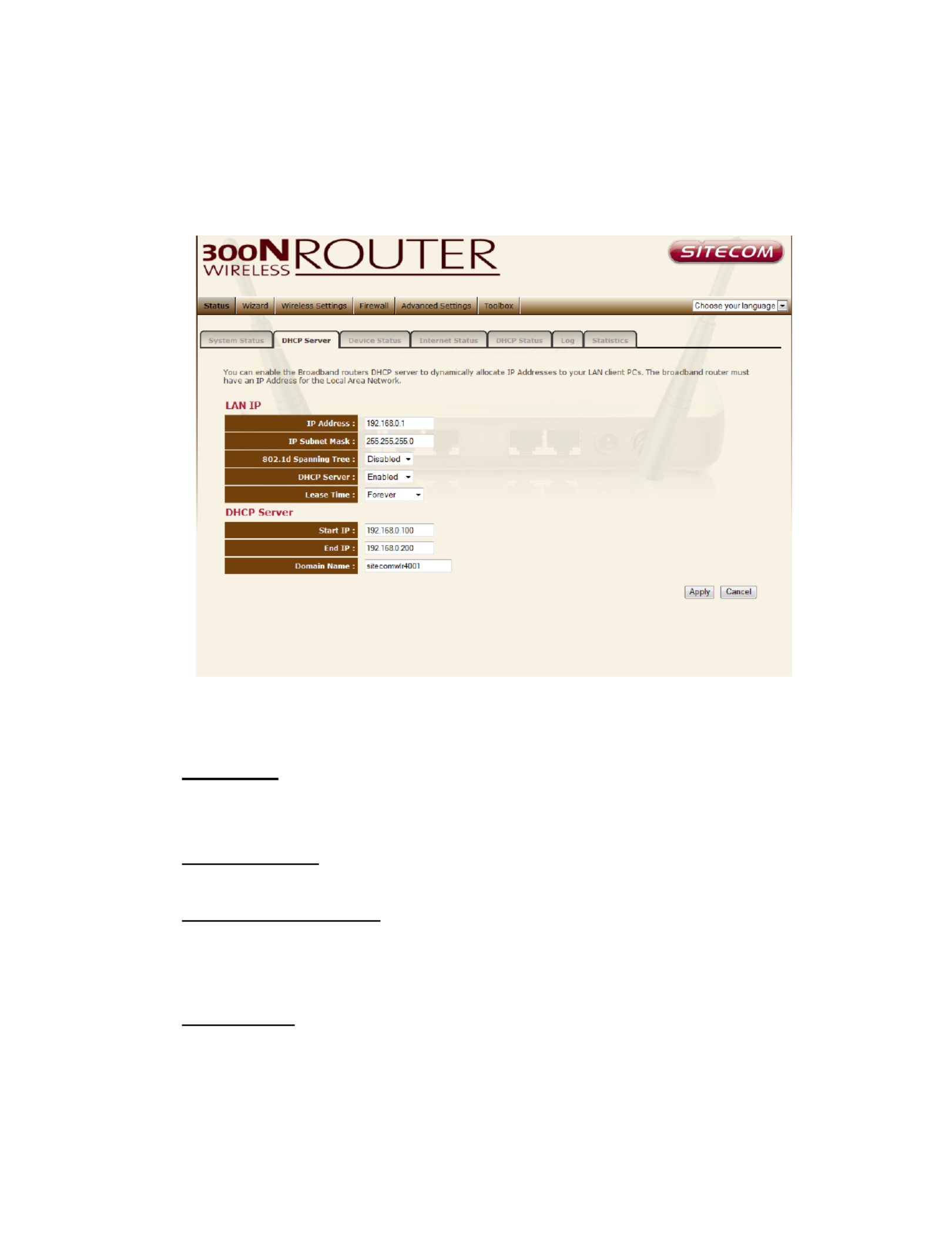
LAN settings
The LAN tab gives you the opportunity to change the IP settings of the WLR-
4003.
Click at the bottom of this screen to save any changes. <Apply>
IP address 192.168.0.1. It is the router‟s LAN IP address (Your LAN clients
default gateway IP address).
IP Subnet Mask 255.255.255.0 Specify a Subnet Mask for your LAN segment.
802.1d Spanning Tree is Disabled by default. If the 802.1d Spanning Tree
function is enabled, this router will use the spanning tree protocol to prevent
network loops.
DHCP Server Enabled by default. You can enable or disable the DHCP server.
When DHCP is disabled no ip-addresses are assigned to clients and you have to
use static ip-addresses. When DHCP server is enabled your computers will be
assigned an ip-address automatically until the lease time expires.

19
Lease Time Forever. In the Lease Time setting you can specify the time period
that the DHCP lends an IP address to your LAN clients. The DHCP will change
your LAN client‟s IP address when this time threshold period is reached.
IP Address Pool You can select a particular IP address range for your DHCP
server to issue IP addresses to your LAN Clients.
Note default IP range is 192.168.0.100 ~ 192.168.0.200. If you want :
your PC(s) to have a static/fixed IP address, then you’ll have to choose
an IP address outside this IP address Pool
Domain Name You can specify a Domain Name for your LAN or just keep the
default (sitecomwlr 4003).

20
Device Status
View the Broadband router‟s current configuration settings. Device Status
displays the configuration settings you‟ve configured in the Wizard / Basic
Settings / Wireless Settings section.

21
Internet Status
This page displays whether the WAN port is connected to a Cable/DSL
connection. It also displays the router‟s WAN IP address, Subnet Mask, and ISP
Gateway as well as MAC address, the Primary DNS. Press the button to Renew
renew your WAN IP address.

23
WLR- Log 4003
View the operation log. This page shows the current system log of the Broadband
router. It displays any event occurred after system start up. At the bottom of the
page, the system log can be saved to a local file for further processing <Save>
or the system log can be cleared or it can be refreshed to <Clear> <Refresh>
get the most updated information. When the system is powered down, the
system log will disappear if not saved to a local file.

24
Statistics
Shows the counters of packets sent and received on WAN, LAN & WLAN.
25
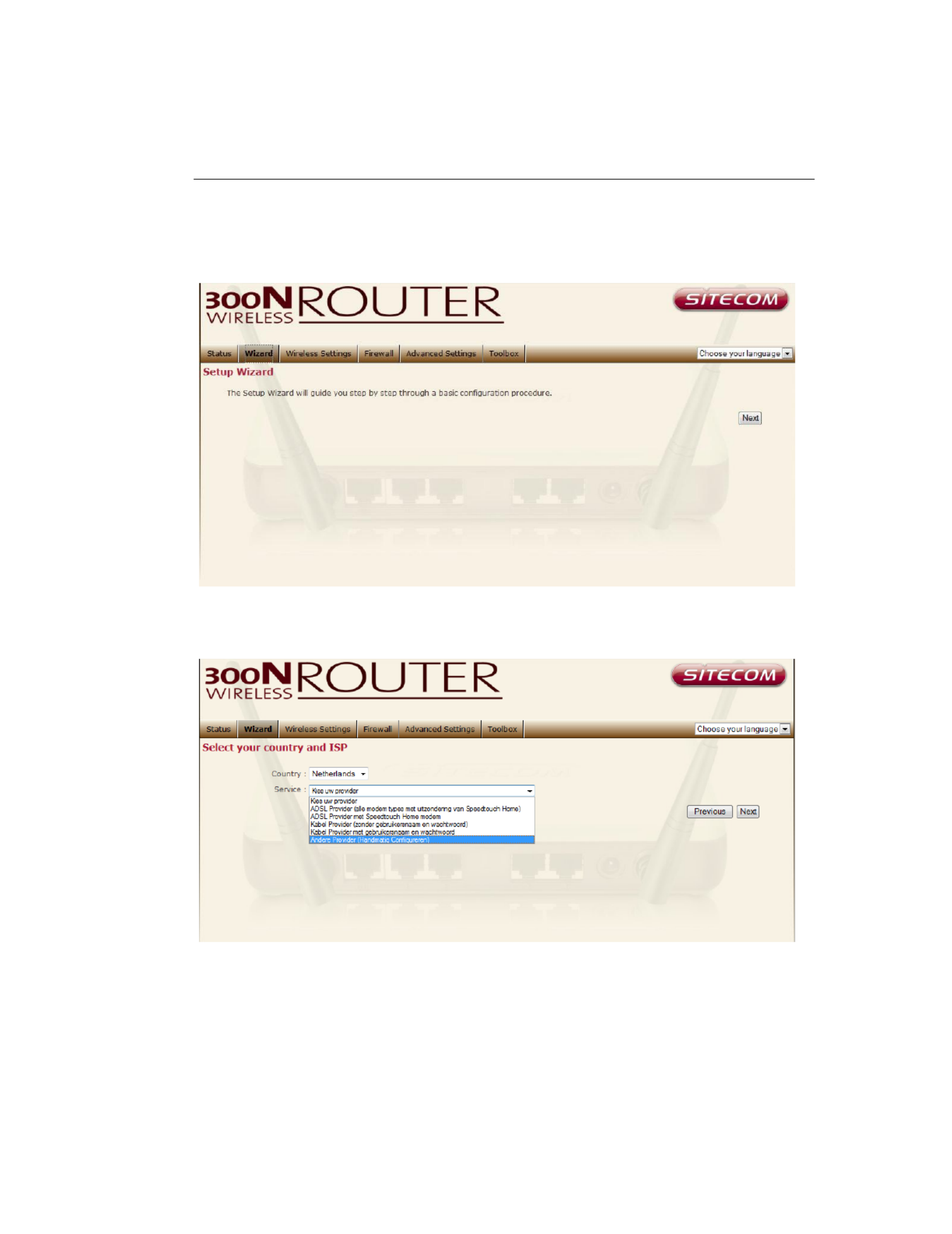
11 Configuration Wizard
Click to configure the router. The Setup wizard will now be displayed; Wizard
check that the modem is connected and click Next.
Select your country from the Country list. Select your internet provider. Click
Next.
26
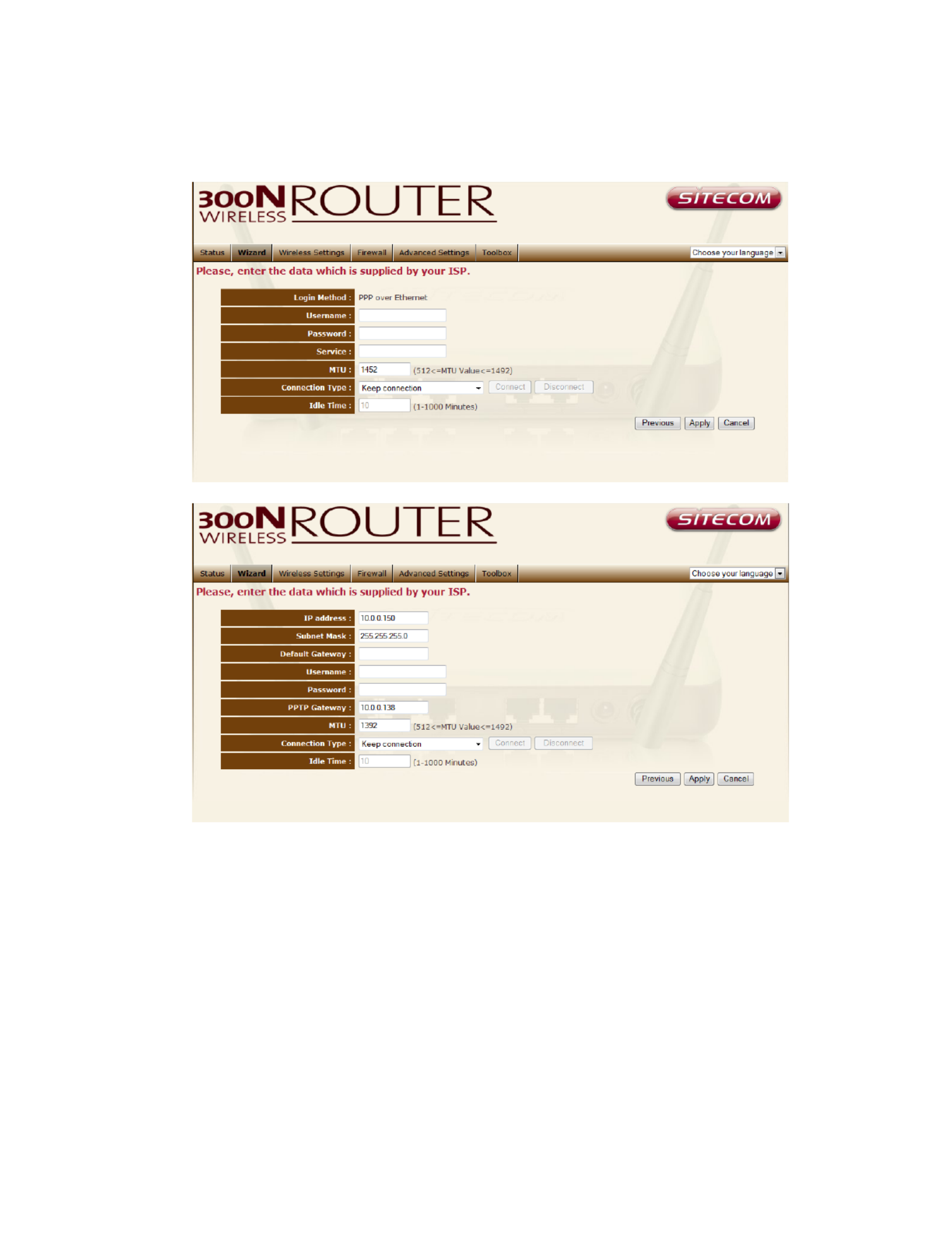
Depending on the chosen provider, you may need to enter your user name
and password, MAC address or hostname in the following window. After you
have entered the correct information, click Next.
Click to complete the configuration. APPLY

27
12 Wireless Settings
You can set parameters that are used for the wireless stations to connect to this
router. The parameters include Mode, ESSID, Channel Number and Associated
Client.
Wireless Function
Enable or Disable Wireless function here. Click and wait for module to Apply
be ready & loaded.

29
Advanced Settings
This tab allows you to set the advanced wireless options. The options included
are Authentication Type, Fragment Threshold, RTS Threshold, Beacon
Interval, and Preamble Type. You should not change these parameters unless
you know what effect the changes will have on the router.
Authentication Type There are two authentication types: "Open System"
and "Shared Key". When you select "Open System", wireless stations can
associate with this wireless router without WEP encryption. When you select
"Shared Key", you should also setup a WEP key in the "Encryption" page.
After this has been done, make sure the wireless clients that you want to
connect to the device are also setup with the same encryption key.
Fragment Threshold "Fragment Threshold" specifies the maximum size of a
packet during the fragmentation of data to be transmitted. If you set this
value too low, it will result in bad performance.
RTS Threshold When the packet size is smaller then the RTS threshold, the
wireless router will not use the RTS/CTS mechanism to send this packet.

30
Beacon Interval is the interval of time that this wireless router broadcasts a
beacon. A Beacon is used to synchronize the wireless network.
Data Rate The “Data Rate” is the rate that this access point uses to transmit
data packets. The access point will use the highest possible selected
transmission rate to transmit the data packets.
N Data Rate The “Data Rate” is the rate that this access point uses to
transmit data packets for N compliant wireless nodes. Highest to lowest data
rate can be fixed.
Channel Bandwidth is the range of frequencies that will be used.
Preamble Type The “Long Preamble” can provide better wireless LAN
compatibility while the “Short Preamble” can provide better wireless LAN
performance.
CTS Protection: It is recommended to enable the protection mechanism.
This mechanism can decrease the rate of data collision between 802.11b and
802.11g wireless stations. When the protection mode is enabled, the
throughput of the AP will be a little lower due to a lot of frame-network that is
transmitted.
TX Power can be set to a bare minimum or maximum power.

31
Security
This Access Point provides complete wireless LAN security functions, included
are WEP, IEEE 802.11x, IEEE 802.11x with WEP, WPA with pre-shared key
and WPA with RADIUS. With these security functions, you can prevent your
wireless LAN from illegal access. Please make sure your wireless stations use
the same security function, and are setup with the same security key.
SSID Selection Here you choose the SSID for which you wish to set the
security.
Broadcast ESSID If you enabled “Broadcast ESSID”, every wireless station
located within the coverage of this access point can discover this access point
easily. If you are building a public wireless network, enabling this feature is
recommended. Disabling “Broadcast ESSID” can provide better security.
WMM WiFi Multi Media if enabled supports QoS for experiencing better audio,
video and voice in applications.
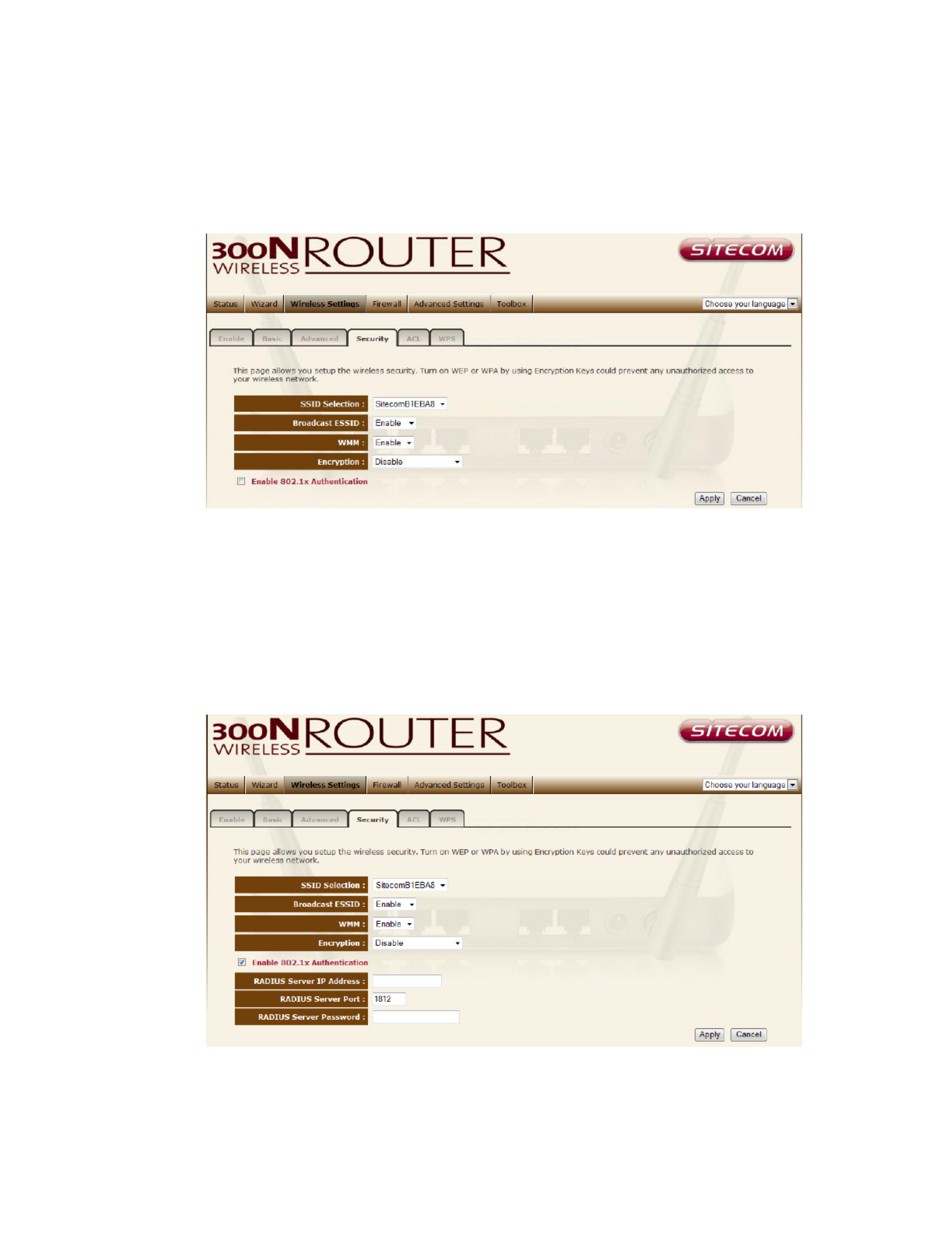
32
Disable
When you choose to disable encryption, it is very insecure to operate the
router.
Enable 802.1x Auth
IEEE 802.1x is an authentication protocol. Every user must use a valid
account to login to this Access Point before accessing the wireless LAN. The
authentication is processed by a RADIUS server. This mode only authenticates
users by IEEE 802.1x, but it does not encrypt the data during communication

33
WEP
When you select 64-bit or 128-bit WEP key, you have to enter WEP keys to
encrypt data. You can generate the key by yourself and enter it. You can
enter four WEP keys and select one of them as a default key. Then the router
can receive any packets encrypted by one of the four keys.
Key Length You can select the WEP key length for encryption, 64-bit or 128-
bit. The larger the key will be the higher level of security is used, but the
throughput will be lower.
Key Format You may select ASCII Characters (alphanumeric format) or
Hexadecimal Digits (in the "A-F", "a-f" and "0-9" range) to be the WEP Key.
Key1 - Key4 The WEP keys are used to encrypt data transmitted in the
wireless network. Use the following rules to setup a WEP key on the device.
64-bit WEP: input 10-digits Hex values (in the "A-F", "a-f" and "0-9" range) or
5-digit ASCII character as the encryption keys. 128-bit WEP: input 26-digit
Hex values (in the "A-F", "a-f" and "0-9" range) or 13-digit ASCII characters
as the encryption keys.

34
Click <Apply> at the bottom of the screen to save the above configurations.
You can now configure other sections by choosing Continue, or choose Apply
to apply the settings and reboot the device.
WPA Pre-shared Key
Wi-Fi Protected Access (WPA) is an advanced security standard. You can use a
pre-shared key to authenticate wireless stations and encrypt data during
communication. It uses TKIP or CCMP (AES) to change the encryption key
frequently. So the encryption key is not easy to be cracked by hackers. This is
the best security available.
WPA-Radius
Wi-Fi Protected Access ( ) is an advanced security standard. You can use WPA
an external RADIUS server to authenticate wireless stations and provide the
session key to encrypt data during communication. It uses or CCMP TKIP
( ) to change the encryption key frequently. Press button when you AES Apply
are done.

35

36
ACL
This wireless router supports MAC Address Control, which prevents
unauthorized clients from accessing your wireless network.
Enable wireless access control Enables the wireless access control function
Adding an address into the list Enter the "MAC Address" and "Comment"
of the wireless station to be added and then click "Add". The wireless station
will now be added into the "Current Access Control List" below. If you are
having any difficulties filling in the fields, just click "Clear" and both "MAC
Address" and "Comment" fields will be cleared.
Remove an address from the list If you want to remove a MAC address
from the "Current Access Control List ", select the MAC address that you want
to remove in the list and then click "Delete Selected". If you want to remove
all the MAC addresses from the list, just click the "Delete All" button. Click
"Reset" will clear your current selections.
Click <Apply> at the bottom of the screen to save the above configurations.
You can now configure other sections by choosing Continue, or choose Apply
to apply the settings and reboot the device.

37
WPS
Wi-Fi Protected Setup (WPS) is the simplest way to establish a connection
between the wireless clients and the wireless router. You don‟t have to select
the encryption mode and fill in a long encryption passphrase every time when
you try to setup a wireless connection. You only need to press a button on
both wireless client and wireless router, and WPS will do the rest for you.
The wireless router supports two types of WPS: WPS via Push Button and
WPS via PIN code. If you want to use the Push Button, you have to push a
specific button on the wireless client or in the utility of the wireless client to
start the WPS mode, and switch the wireless router to WPS mode. You can
simply push the WPS button of the wireless router, or click the „Start to
Process‟ button in the web configuration interface. If you want to use the PIN
code, you have to know the PIN code of the wireless client and switch it to
WPS mode, then fill-in the PIN code of the wireless client through the web
configuration interface of the wireless router.

39
13 Firewall Settings
The Broadband router provides extensive firewall protection by restricting
connection parameters, thus limiting the risk of hacker attacks, and defending
against a wide array of common Internet attacks. However, for applications that
require unrestricted access to the Internet, you can configure a specific
client/server as a Demilitarized Zone (DMZ).
Note: To enable the Firewall settings select Enable and click Apply

40
DMZ
If you have a client PC that cannot run an Internet application (e.g. Games)
properly from behind the NAT firewall, then you can open up the firewall
restrictions to unrestricted two-way Internet access by defining a DMZ Host.
The DMZ function allows you to re-direct all packets going to your WAN port
IP address to a particular IP address in your LAN. The difference between the
virtual server and the DMZ function is that the virtual server re-directs a
particular service/Internet application (e.g. FTP, websites) to a particular LAN
client/server, whereas DMZ re-directs all packets (regardless of services)
going to your WAN IP address to a particular LAN client/server.
Enable DMZ Enable/disable DMZ
Public IP Address The IP address of the WAN port or any other Public IP
addresses given to you by your ISP
Client PC IP Address -in the IP address of a particular host in your LAN Fill
that will receive all the packets originally going to the WAN port/Public IP
address above.
Click at the bottom of the screen to save the above configurations. <Apply>

41
Denial of Service (DoS)
The Broadband router's firewall can block common hacker attacks, including
Denial of Service, Ping of Death, Port Scan and Sync Flood. If Internet attacks
occur the router can log the events.
Ping of Death Protections from Ping of Death attack
Discard Ping From WAN The router‟s WAN port will not respond to any Ping
requests
Port Scan Protects the router from Port Scans.
Sync Flood Protects the router from Sync Flood attack.
42
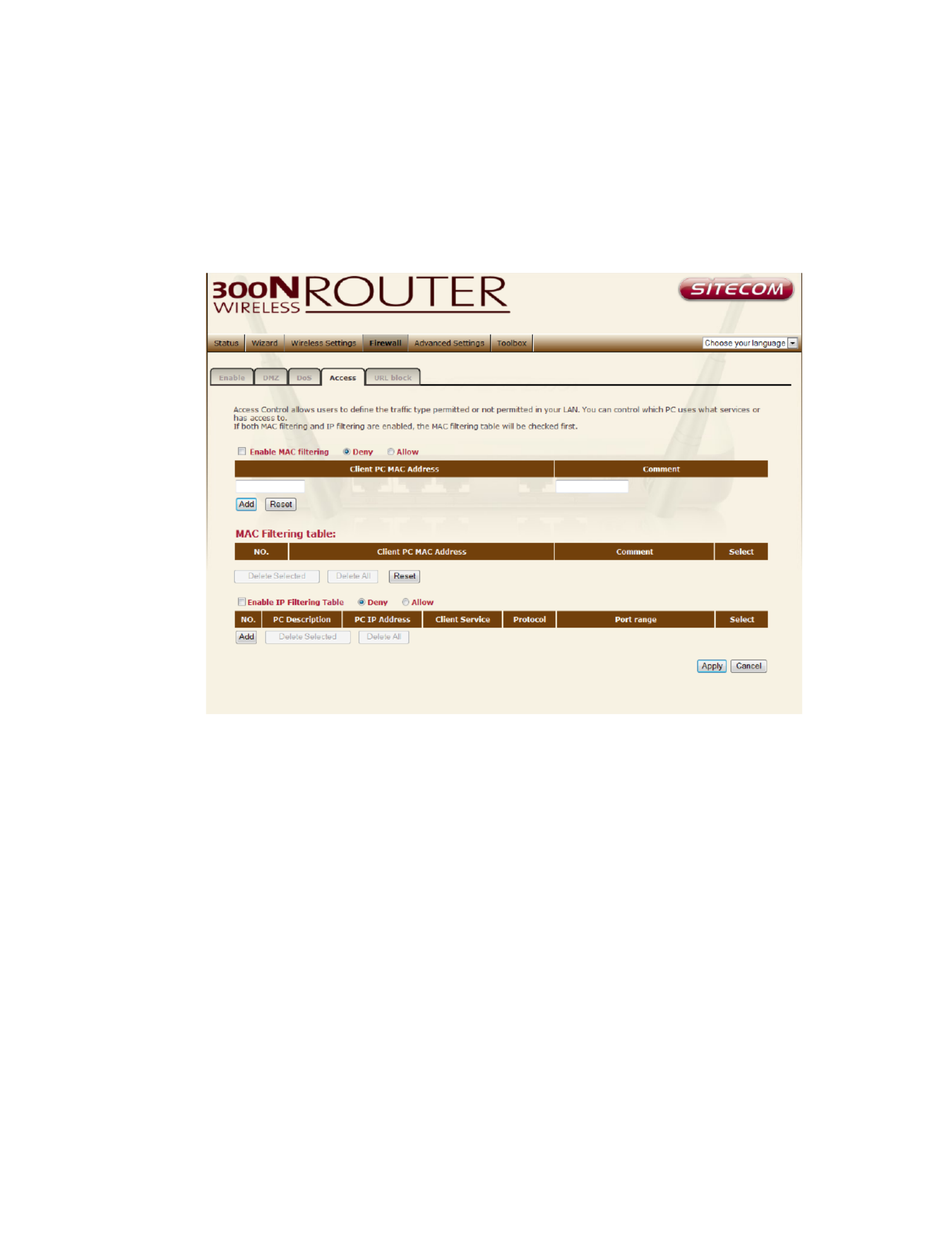
Access
You can restrict users from accessing certain Internet applications/services
(e.g. Internet websites, email, FTP etc.), Access Control allows users to define
the traffic type permitted in your LAN. You can control which PC client can
have access to these services.
Deny If you select “Deny” then all clients will be allowed to access Internet
accept for the clients in the list below.
Allow If you select “Allow” then all clients will be denied to access Internet
accept for the PCs in the list below.
Filter client PCs by IP Fill in “IP Filtering Table” to filter PC clients by IP.
Add PC You can click Add PC to add an access control rule for users by IP
addresses.
Remove PC If you want to remove some PCs from the "IP Filtering Table",
select the PC you want to remove in the table and then click “Delete

43
Selected". If you want to remove all PCs from the table, just click the "Delete
All" button.
Filter client PC by MAC Check “Enable MAC Filtering” to enable MAC
Filtering.
Add PC Fill in “Client PC MAC Address” and “Comment” of the PC that is
allowed to access the Internet, and then click “Add”. If you find any typo
before adding it and want to retype again, just click "Reset" and the fields will
be cleared.
Remove PC If you want to remove some PC from the "MAC Filtering Table",
select the PC you want to remove in the table and then click "Delete
Selected". If you want to remove all PCs from the table, just click the "Delete
All" button. If you want to clear the selection and re-select again, just click
“Reset”.
Click < > at the bottom of the screen to save the above configuration. Apply

44
URL block
You can block access to some Web sites from particular PCs by entering a full
URL address or just keywords of the Web site.
Enable URL Blocking Enable/disable URL Blocking
Add URL Keyword Fill in “URL/Keyword” and then click “Add”. You can enter
the full URL address or the keyword of the web site you want to block.
Remove URL Keyword If you want to remove some URL keywords from the
"Current URL Blocking Table", select the URL keyword you want to remove in
the table and then click "Delete Selected". If you want remove all URL
keywords from the table, just click "Delete All" button. If you want to clear
the selection and re-select again, just click “Reset”.
Click < > at the bottom of the screen to save the above configurations Apply

45
14 Advanced Settings
Network Address Translation (NAT) allows multiple users at your local site to
access the Internet through a single Public IP Address or multiple Public IP
Addresses. NAT provides Firewall protection from hacker attacks and has the
flexibility to allow you to map Private IP Addresses to Public IP Addresses for
key services such as Websites and FTP. Select Disable to disable the NAT
function.

48
Virtual Server
Use the Virtual Server function when you want different servers/clients in
your LAN to handle different service/Internet application type (e.g. Email,
FTP, Web server etc.) from the Internet. Computers use numbers called port
numbers to recognize a particular service/Internet application type. The
Virtual Server allows you to re-direct a particular service port number (from
the Internet/WAN Port) to a particular LAN private IP address and its service
port number.
Enable Virtual Server Enable Virtual Server.
Private IP This is the LAN client/host IP address that the Public Port number
packet will be sent to.
Private Port This is the port number (of the above Private IP host) that the
below number will be changed to when the packet enters your Public Port
LAN (to the LAN Server/Client IP)
Type Select the port number protocol type (TCP, UDP or both). If you are
unsure, then leave it to the default “both” setting. Public Port Enter the

49
service (service/Internet application) port number from the Internet that will
be re-directed to the above Private IP address host in your LAN
Comment The description of this setting.
Add Virtual Server Fill in the "Private IP", "Private Port", "Type", “Public
Port” and "Comment" of the setting to be added and then click "Add". Then
this Virtual Server setting will be added into the "Current Virtual Server Table"
below.
Remove Virtual Server If you want to remove Virtual Server settings from
the "Current Virtual Server Table", select the Virtual Server settings you want
to remove in the table and then click "Delete Selected". If you want to
remove all Virtual Server settings from the table, just click the "Delete All"
button. Click "Reset" will clear your current selections.
Click < > at the bottom of the screen to save the above configurations. Apply

50
Special Applications
Some applications require multiple connections, such as Internet games,
video Conferencing, Internet telephony and others. In this section you can
configure the router to support multiple connections for these types of
applications.
Enable Trigger Port Enable the Special Application function.
Trigger Port This is the out going (Outbound) range of port numbers for this
particular application.
Trigger Type Select whether the outbound port protocol is “TCP”, “UDP” or
both.
Public Port Enter the In-coming (Inbound) port or port range for this type of
application (e.g. 2300-2400, 47624)
Public Type Select the Inbound port protocol type: “TCP”, “UDP” or both
Comment The description of this setting.

51
Popular applications This section lists the more popular applications that
require multiple connections. Select an application from the Popular
Applications selection. Once you have selected an application, select a
location (1-10) in the Copy to selection box and then click the Copy to button.
This will automatically list the Public Ports required for this popular application
in the location (1-10) you specified.
Add Special Application Fill in the "Trigger Port", "Trigger Type”, “Public
Port”, "Public Type", "Public Port" and "Comment" of the setting to be added
and then click "Add". The Special Application setting will be added into the
"Current Trigger-Port Table" below. If you happen to make a mistake, just
click "Clear" and the fields will be cleared.
Remove If you want to remove Special Application settings from the "Current
Trigger-Port Table", select the Special Application settings you want to remove
in the table and then click "Delete Selected". If you want remove all Special
Application settings from the table, just click the "Delete All" button. Click
"Reset" will clear your current selections.

52
UPnP
With UPnP, all PCs in you Intranet will discover this router automatically, so
you don‟t have to configure your PC and it can easily access the Internet
through this router.
UPnP Feature You can enable or Disable the UPnP feature here. After you
enable the UPnP feature, all client systems that support UPnP, like Windows
XP, can discover this router automatically and access the Internet through this
router without having to configure anything. The NAT Traversal function
provided by UPnP can let applications that support UPnP connect to the
internet without having to configure the virtual server sections.

53
QoS
QoS can let you classify Internet application traffic by source/destination IP
address and port number. You can assign priority for each type of application
and reserve bandwidth for it. The packets of applications with higher priority
will always go first. Lower priority applications will get bandwidth after higher
priority applications get enough bandwidth. This can let you have a better
experience in using critical real time services like Internet phone, video
conference …etc. All the applications not specified by you are classified as rule
name “Others”. The rule with a smaller priority number has a higher priority;
the rule with a larger priority number has a lower priority. You can adjust the
priority of the rules by moving them up or down.
Enable/Disable QoS You can check “Enable QoS” to enable QoS
functionality for the WAN port.
Add a QoS rule into the table Click “Add” then enter a form of the QoS
rule. Click “Apply” after filling out the form the rule will be added into the
table.

54
Remove QoS rules from the table If you want to remove QoS rules from
the table, select the QoS rules you want to remove in the table and then click
"Delete Selected". If you want remove all QoS rules from the table, just click
the "Delete All" button. Clicking "Reset" will clear your current selections.
Edit a QoS rule Select the rule you want to edit and click “Edit”, then enter
the detail form of the QoS rule. Click “ ” after editing the form and the Apply
rule will be saved.
Adjust QoS rule priority You can select the rule and click “Move Up” to
make its priority higher. You also can select the rule and click “Move Down” to
make its priority lower.

55
15 TOOLBOX Settings
Sitecom Cloud Security
Antivirus software alone is not safe enough. You can now benefit from
additional built-in security in your modem or router. Protect all devices in your
home network against cybercrime while browsing. Activated automatically,
your network and devices are better secured than ever before.
Your Sitecom device comes with a 6 month free Sitecom cloud security
subscription.
After you have set up your Sitecom device for internet access, open the web
browser and enter http://www.sitecomcloudsecurity.com in the address bar.
If the device has been properly configured the following web page should be
shown.
Here you can see which security features are activated.

56
The service offers the following protection options: Sitecom oud curity Cl Se
Anti-Malware
Anti-Phishing
Protection against unsafe websites
Advertisement blocking
With the protection of activated the Sunsafe websites itecom Cloud Security
will always check if a website is safe. If it is not safe it will inform you that is
not safe to enter.
If you still wish to visit this webpage click on „proceed anyway‟. Alternatively
click „Back to Safety‟ so that your security will not be breached.

59
found on the back label on the bottom of your Sitecom device).
Go to Toolbox and select “Sitecom Cloud Security”.
Click the “Disable” radio button and click „Apply‟ for the settings to take effect.

60
Password change options
You can change the password required to log into the broadband router's
system web-based management. Passwords can contain 0 to 12 alphanumeric
characters, and are case sensitive.
Current Password Fill in the current password to allow changing to a new
password.
New Password Enter your new password.
Confirmed Password Enter your new password again for verification
purposes.
Click < > at the bottom of the screen to save the above configurations Apply

61
Time Zone
The Time Zone allows your router to base its time on the settings configured
here, which will affect functions such as Log entries and Firewall settings.
Set Time Zone Select the time zone of the country you are currently in. The
router will set its time based on your selection.
Time Server Address You can set an NTP server address.
Enable Daylight Savings The router can also take Daylight savings into
account. If you wish to use this function, you must check/tick the enable box
to enable your daylight saving configuration (below).
Start Daylight Savings Time Select the period in which you wish to start
daylight Savings Time
End Daylight Savings Time Select the period in which you wish to end
daylight Savings Time
Click < > at the bottom of the screen to save the above configurations Apply
Termékspecifikációk
| Márka: | Sitecom |
| Kategória: | router |
| Modell: | WLR-4003 |
Szüksége van segítségre?
Ha segítségre van szüksége Sitecom WLR-4003, tegyen fel kérdést alább, és más felhasználók válaszolnak Önnek
Útmutatók router Sitecom

2 Október 2024

23 Szeptember 2024

22 Szeptember 2024

20 Szeptember 2024

19 Szeptember 2024

15 Szeptember 2024

30 Augusztus 2024

26 Augusztus 2024

17 Augusztus 2024

16 Augusztus 2024
Útmutatók router
- router Samsung
- router Acer
- router Milwaukee
- router Bosch
- router AEG
- router StarTech.com
- router Einhell
- router Nokia
- router HP
- router Makita
- router BenQ
- router Apple
- router Ubiquiti Networks
- router Siemens
- router TP-Link
- router Medion
- router Motorola
- router Vimar
- router LogiLink
- router Alcatel
- router Roland
- router TCL
- router Digitus
- router Zebra
- router Xiaomi
- router TRENDnet
- router Mercusys
- router AVM
- router EZVIZ
- router Dell
- router Lancom
- router Strong
- router Gigabyte
- router Conceptronic
- router Thomson
- router Juniper
- router Kyocera
- router Hikvision
- router Keewifi
- router Vivanco
- router Netgear
- router Huawei
- router Asus
- router Vtech
- router Hama
- router Zoom
- router Renkforce
- router Synology
- router Draytek
- router Iogear
- router Güde
- router Hitachi
- router Mikrotik
- router Toolcraft
- router ZyXEL
- router SPL
- router Dahua Technology
- router Smart-AVI
- router Black & Decker
- router Devolo
- router Planet
- router Tenda
- router BT
- router Black Box
- router MSI
- router Gembird
- router Cisco
- router PowerPlus
- router ATen
- router Google
- router Metabo
- router Bea-fon
- router ZTE
- router Edimax
- router Vodafone
- router ModeCom
- router HiKOKI
- router Foscam
- router Milan
- router Manhattan
- router Kogan
- router Festool
- router EnGenius
- router Sigma
- router Western Digital
- router D-Link
- router Media-Tech
- router Blustream
- router Milesight
- router Moxa
- router Sagem
- router Razer
- router Trust
- router Porter-Cable
- router Konig
- router Alfa
- router MuxLab
- router DeWalt
- router AVMATRIX
- router IFM
- router A-NeuVideo
- router Atlona
- router Schneider
- router AJA
- router Lindy
- router Cudy
- router Barco
- router QNAP
- router NEC
- router Silverline
- router Cotech
- router Siig
- router Gefen
- router Kathrein
- router Avenview
- router Lantronix
- router Technicolor
- router FSR
- router Topcom
- router Holzmann
- router Arris
- router Anker
- router I-TEC
- router Keenetic
- router Linksys
- router Teltonika
- router Intelix
- router Comprehensive
- router Ocean Matrix
- router Digitalinx
- router Alfatron
- router Belkin
- router RGBlink
- router Kopul
- router KanexPro
- router Key Digital
- router Kramer
- router BZBGear
- router UPC
- router Allnet
- router Allied Telesis
- router Airlive
- router Proximus
- router Skil
- router Eminent
- router Nilox
- router Sonos
- router Patton
- router Techly
- router Totolink
- router KPN
- router Netis
- router Envivo
- router Buffalo
- router Nest
- router LevelOne
- router ICIDU
- router Clas Ohlson
- router AT&T
- router Sweex
- router Aruba
- router Phicomm
- router Kasda
- router Jung
- router Digi
- router Verizon
- router Billion
- router T-Mobile
- router RAVPower
- router Hawking Technologies
- router Nexxt
- router Beafon
- router Kraun
- router LTS
- router Zolid
- router Sagemcom
- router Telstra
- router Eero
- router Advantech
- router Mercku
- router Hercules
- router Xantech
- router Intellinet
- router Arcadyan
- router Digiconnect
- router Ubee
- router SMC
- router Tele 2
- router Peak
- router CradlePoint
- router Davolink
- router Sixnet
- router 7inova
- router AVPro Edge
- router F-Secure
- router Rosewill
- router Digicom
- router Sabrent
- router On Networks
- router PENTAGRAM
- router Leoxsys
- router Readynet
- router OneAccess
- router Accelerated
- router Nexaira
- router Hamlet
- router Approx
- router T-com
- router Amped Wireless
- router Cambium Networks
- router 3Com
- router WyreStorm
- router Ruckus Wireless
- router Dovado
- router Mach Power
- router EXSYS
- router NetComm
- router Comtrend
- router Premiertek
- router GL.iNet
- router Shinybow
- router Edgewater
- router Atlantis Land
- router Lumantek
- router Starlink
- router PulseAudio
- router Predator
- router Evolution
- router Luxul
- router StarIink
- router Silentwind
- router Keezel
- router United Telecom
- router Wisetiger
Legújabb útmutatók router
9 Április 2025

9 Április 2025

9 Április 2025

31 Március 2025

30 Március 2025

30 Március 2025

30 Március 2025

30 Március 2025

30 Március 2025

23 Március 2025